Put the following in the MOTD file:
<script>
if (location.href.indexOf("?") < 0) {
location.href = location.href.replace(/(https?:\/\/[^\/]+)(\/.*)?/, "$1/SPNEGO.po");
}
</script>The same can be done for SAML.po
Put the following in the MOTD file:
<script>
if (location.href.indexOf("?") < 0) {
location.href = location.href.replace(/(https?:\/\/[^\/]+)(\/.*)?/, "$1/SPNEGO.po");
}
</script>The same can be done for SAML.po
Safari mobile 15+ uses desktop mode by default, if desired disable it in;
Wikipedia has a list. Comments on the popular options;
Micro services; fast start with native executables via GraalVM;
Specifications at jakarta.
To display timestamps exported from Noodle to csv files in Microsoft Excel, format the column as custom with this pattern;
yyyy-mm-dd hh:mm:ss.000To show just the date one of these formulae can be used;
=DATE(YEAR(B2),MONTH(B2),DAY(B2))
=CONCAT(YEAR(B2),"-",MONTH(B2),"-",DAY(B2))To show just the time one of these formulae can be used;
=TIME(HOUR(B2),MINUTE(B2),SECOND(B2))
=CONCAT(HOUR(B2),":",MINUTE(B2),":",SECOND(B2))Like all formula the above examples can be applied to whole columns by copy pasting, dragging, or double clicking.
Note that Microsoft Excel does not respect original formatting so any save (without any edit) can convert a timestamp into a number representing seconds since epoch.
certbot renew --quiet --manual --preferred-challenges dns \
--manual-public-ip-logging-ok \
--manual-auth-hook cert_dns.sh \
--deploy-hook cert_deploy.shssh $DNS "nsupdate <( echo \"server 127.0.0.1
update delete _acme-challenge.$CERTBOT_DOMAIN.
update add _acme-challenge.$CERTBOT_DOMAIN. 3600 TXT $CERTBOT_VALIDATION
send
quit\" )"
sleep 10See letsencrypt for other options.
sed -i -e 's/#\(.*[0-9]\/com\)/\1/g' /etc/apk/repositories
apk update
apk add openjdk11 postgresql postgresql-contrib
service postgresql start
#Noodle
cd /opt
tar -xf Noodle.tar.gz
cd Noodle
su postgres -c 'cd;psql --file /opt/Noodle/init.sql'
mv noodle.openrc /etc/init.d/noodle
service noodle startOther Linux Installation examples available.
dnf install -y epel-release
dnf install -y tar postgresql-server postgresql-contrib java-11-openjdk
#optional
dnf install -y vim tmux bc id3lib html2text p7zip-plugins libjpeg-turbo poppler-utils unzip netpbm-progs perl-Image-ExifTool
#optional manual install catdoc unrtf ffmpeg
newcfg (){
F="$1"
chown --reference="$F" "$F".new
chmod --reference="$F" "$F".new
mv -f "$F".new "$F"
}
#PostgreSQL
/usr/bin/postgresql-setup --initdb --unit postgresql
systemctl enable postgresql
TMP=/var/lib/pgsql/data/pg_hba.conf
cp $TMP $TMP.original
cat $TMP | grep -vP "^ *host.*127" > $TMP.new
echo -e "host\tall\tall\t127.0.0.1/32\tpassword" >> $TMP.new
newcfg $TMP
TMP=/var/lib/pgsql/data/postgresql.conf
cp $TMP $TMP.original
MT=$(cat /proc/meminfo | grep MemTotal | perl -pe 's/^[^ ]* *([0-9]+) *kB$/$1\/1000/g');
#java+linux=(512+256)
ECS=$(echo "($MT-(512+256))/2" | bc);
SB=$(echo "($MT-(512+256))/4" | bc);
cat $TMP | perl -pe 's/^#?(effective_cache_size)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = '$ECS'MB$2/g' \
| perl -pe 's/^#?(shared_buffers)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = '$SB'MB$2/g' \
| perl -pe 's/^#?(max_locks_per_transaction)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = 512$2/g' \
| perl -pe 's/^#?(max_connections)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = 60$2/g' \
| perl -pe 's/^#?(checkpoint_segments)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = 30$2/g' \
| perl -pe 's/^#?(log_min_duration_statement)[ \t]*=[ \t]*[^ \t]+([ \t].*)?$/$1 = 30000$2/g' \
| perl -pe 's/^#?(log_line_prefix)[ \t]*=[ \t]*[^#]+(#.*)?$/$1 = '\''%m: '\''\t\t$2/g' \
> $TMP.new
newcfg $TMP
systemctl start postgresql
#Noodle
cd /opt
tar -zxf ./Noodle.tar.gz
su postgres -c 'cd;/usr/bin/psql -d postgres -U postgres --file /opt/Noodle/init.sql'
cd Noodle
cp noodle.service /lib/systemd/system/
systemctl enable noodle
systemctl start noodleOther Linux Installation examples available.
Noodle respects requests for dark mode with the "prefers-color-scheme:dark" CSS that can be customized.
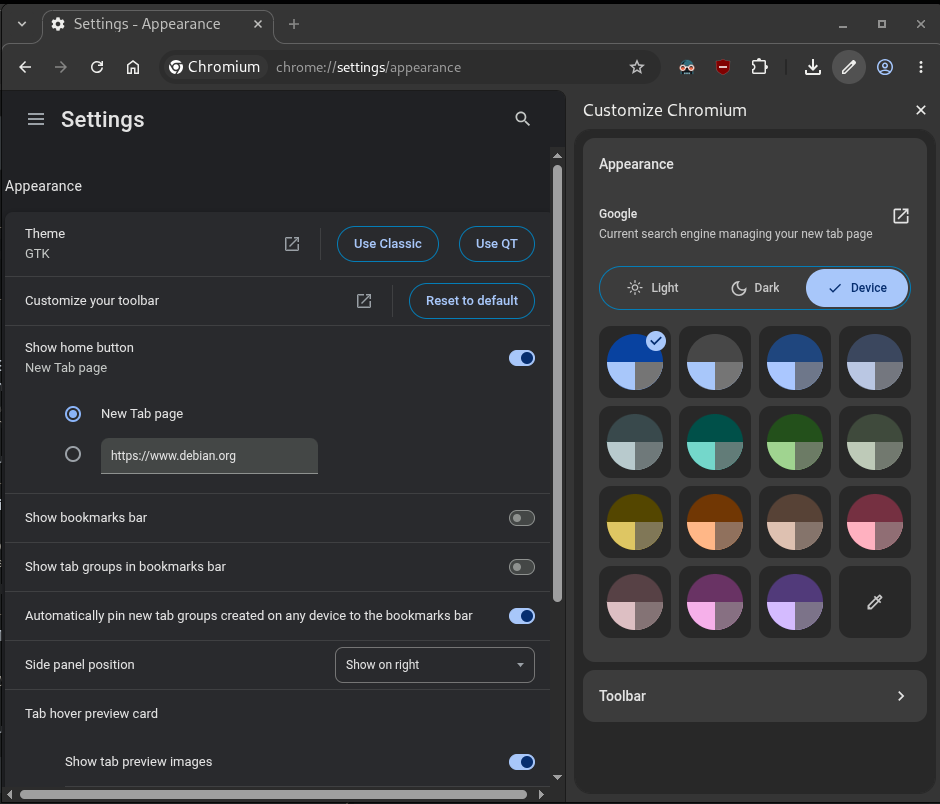
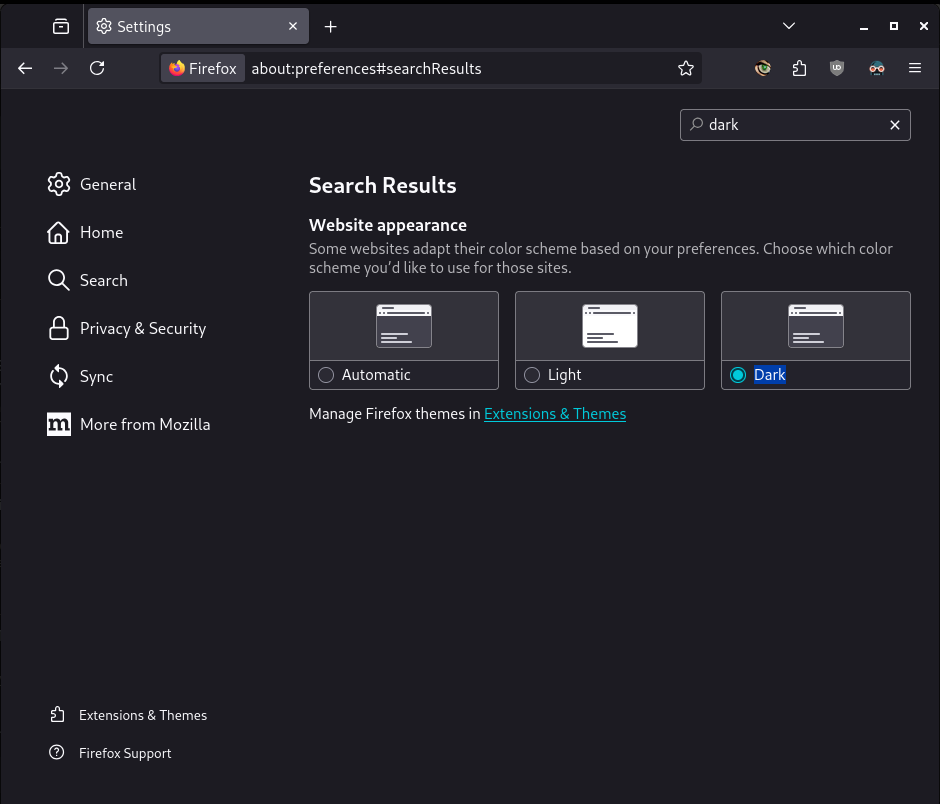
Web Browsers respect requests for dark mode by the Operating System, and can be customized:
Operating Systems can be customized to use dark mode:
Other sites that support dark mode as of 2020:
Other sites that support dark mode as of 2025:
Any user with access to system tools can reset the admin password with a web browser.
Any person with access to the SQL server can change the admin password to another users password
select object_id, username, password from users where username = 'admin' or username = '$ME';
update users set password = '$PASS' where object_id = '$ID';For example
update users set password = 'P3b*cH.5fOBTJl5ELM)W' where username = 'admin';Criteria | Conformance Level | Remarks and Explanations | |||
1.1.1 Non-text Content (Level A) | Supports | All buttons have descriptive title attributes or text content | |||
| Supports | Notifications use Operating System visual alters to complement audio alters. Audio alerts can be disabled. | ||||
1.2.2 Captions (Prerecorded) (Level A) | Not Applicable | No audio/video content is included, users are responsible for making their own content compliant. Means are available for pre-recorded and live descriptions, subtitles, and sign language content. | |||
1.2.3 Audio Description or Media Alternative (Prerecorded) (Level A) | Not Applicable | " | |||
1.3.1 Info and Relationships (Level A) | Supports | With multiple text application views, and APIs data relationships are programmatically determinable. | |||
1.3.2 Meaningful Sequence (Level A) | Supports | " | |||
1.3.3 Sensory Characteristics (Level A) | Supports | See 1.1.1 Remarks. | |||
1.4.1 Use of Color (Level A) | Supports | The default style sheet is high contrast. Color indicators are accompanied by icons and text. Color indicators can be disabled. User created content has automatic contrast assist (posters). Maximum contrast styles can be achieved with custom style sheets or options. | |||
1.4.2 Audio Control (Level A) | Supports | Audio alerts can be disabled. User uploaded media has default controls including volume. (As of 2020 individual web-cam/screen-share volume is supported in Chrome not Firefox) | |||
2.1.1 Keyboard (Level A) | Supports | All actions are achievable with [shift]tab,space,return. | |||
2.1.2 No Keyboard Trap (Level A) | Supports | No Keyboard Traps are present. | |||
2.1.4 Character Key Shortcuts (Level A 2.1 only) | Supports | No Key Shortcuts are defined. Default shortcuts (copy/paste) are not disabled. | |||
2.2.1 Timing Adjustable (Level A) | Supports | Login session time limit can be changed and disabled. TOTP has a fixed limit but is optional. | |||
2.2.2 Pause, Stop, Hide (Level A) | Supports | There is no moving, scrolling information. Blinking, and auto-updating information can be stopped and scrolled respectively, and is only used where necessary in optional live feeds. | |||
2.3.1 Three Flashes or Below Threshold (Level A) | Supports | Title bar notification flash can be disabled and updates every 1/2 a second when enabled. | |||
2.4.1 Bypass Blocks (Level A) | Supports | Content Blocks are not repeated. | |||
2.4.2 Page Titled (Level A) | Supports | Meaningful Titles are displayed | |||
2.4.3 Focus Order (Level A) | Supports | navigation sequences does not affect meaning. | |||
2.4.4 Link Purpose (In Context) (Level A) | Supports | Link purpose can be equally determined from context programmatically and generally. | |||
2.5.1 Pointer Gestures (Level A 2.1 only) | Supports | Multi-point and path-based gestures have alternatives (widget order via drag and admin down button, zoom via pinch and tap and click). All can be disabled. | |||
2.5.2 Pointer Cancellation (Level A 2.1 only) | Supports | All persistent actions have an Abort option and or undo action.All actions that use a down event by requirement (drag and drop) have alternatives (order and upload buttons). | |||
2.5.3 Label in Name (Level A 2.1 only) | Supports | All user interface components contain text by which software can identify it to the user. | |||
2.5.4 Motion Actuation (Level A 2.1 only) | Supports | See 2.5.1 Remarks. | |||
3.1.1 Language of Page (Level A) | Supports | The lang attribute is used on all pages. | |||
3.2.1 On Focus (Level A) | Supports | Focus has no context change (Notifications can be suppressed on focus) | |||
3.2.2 On Input (Level A) | Supports | Setting changes (without submit button use ) will not change context. | |||
3.3.1 Error Identification (Level A) | Supports | On input error detection, a text description is shown and where convenient the input focused | |||
3.3.2 Labels or Instructions (Level A) | Supports | Labels or instructions are provided for user input, and also for user generated user input. | |||
4.1.1 Parsing (Level A) | Supports | markup conforms to specification. | |||
4.1.2 Name, Role, Value (Level A) | Supports | " | |||
Criteria | Conformance Level | Remarks and Explanations | |||
1.2.4 Captions (Live) (Level AA) | Not Applicable | See 1.2.2 Remarks. | |||
1.2.5 Audio Description (Prerecorded) (Level AA) | Not Applicable | " | |||
1.3.4 Orientation (Level AA 2.1 only) | Supports | Content flows, with minimal fixed width components. | |||
1.3.5 Identify Input Purpose (Level AA 2.1 only) | Supports | programmatic Identification of Input Purpose can be achieved with placeholders, names, and previous elements. | |||
1.4.3 Contrast (Minimum) (Level AA) | Supports | See 1.4.1 Remarks. | |||
1.4.4 Resize text (Level AA) | Supports | 300% text size is supported on 4k screens, mobile UI uses large text by default. | |||
1.4.5 Images of Text (Level AA) | Supports | No images of text are used. | |||
1.4.10 Reflow (Level AA 2.1 only) | Supports | 320 pixel width is supported via the mobile and top-navigation interfaces. | |||
1.4.11 Non-text Contrast (Level AA 2.1 only) | Supports | See 1.4.1 Remarks. | |||
1.4.12 Text Spacing (Level AA 2.1 only) | Supports | 2x default text spacing is supported via zoom, custom CSS, or plugins. | |||
1.4.13 Content on Hover or Focus (Level AA 2.1 only) | Supports | Custom tooltips are inlined when no pointer is detected or by option. selection and focus are supported. q will dismiss. | |||
2.4.5 Multiple Ways (Level AA) | Supports | With multiple application views, content views, and navigation options, in addition to quick links, external links, and custom user links Multiple Ways are supported. | |||
2.4.6 Headings and Labels (Level AA) | Supports | Standardized Headings and Labels are used to make page purpose intuitive and programmatically identifiable. | |||
2.4.7 Focus Visible (Level AA) | Supports | Keyboard focus is visible and adjustable with custom CSS (a:focus-visible,input:focus-visible{border:solid 5px red}) | |||
3.1.2 Language of Parts (Level AA) | Supports | Part language can differ from page language only via user input and that accepts tagging for programmatic use for the body of the content. the language of user input titles does not support direct language tags for programmatic use. A custom script can be used to tag persistent multi language features if required. | |||
3.2.3 Consistent Navigation (Level AA) | Supports | Navigation including order is persistent (and can be customized to sort alphabetically, by date, or in a custom order) | |||
3.2.4 Consistent Identification (Level AA) | Supports | Buttons/Links of different types are identifiable by class (navigation vs persistent action) | |||
3.3.3 Error Suggestion (Level AA) | Supports | Error Suggestions are avoided by limiting input to begin with (entering text in a numeric, invalid dates, etc) | |||
| Supports | Legal and Financial Data are not used, but input is reviewable, and reversible. (instant messenger can be disabled to support only reversible content), input validation is performed before submission when supported. trash/recycle bin, and remove/purge of content is confirmed. | ||||
4.1.3 Status Messages (Level AA 2.1 only) | Supports | Status messages can be identified by class. | |||
Criteria | Conformance Level | Remarks and Explanations | |||
1.2.6 Sign Language (Prerecorded) (Level AAA) | Not Applicable | See 1.2.2 Remarks. | |||
1.2.7 Extended Audio Description (Prerecorded) (Level AAA) | Not Applicable | " | |||
1.2.8 Media Alternative (Prerecorded) (Level AAA) | Not Applicable | " | |||
1.2.9 Audio-only (Live) (Level AAA) | Not Applicable | " | |||
1.3.6 Identify Purpose (Level AAA 2.1 only) | Supports | User Interface Components can be programmatically determined via attribute naming conventions. | |||
1.4.6 Contrast (Enhanced) (Level AAA) | Supports | See 1.4.1 Remarks. | |||
1.4.7 Low or No Background Audio (Level AAA) | Supports | See 1.4.2 Remarks. | |||
1.4.8 Visual Presentation (Level AAA) | Partially Supports | Colors are user select-able. Width can be under 80 characters with the mobile view. The justify text alignment is not used. Line and paragraph spacing are default and adjustable. Text can be resized without assistive technology up to 200 percent in a way that does not require the user to scroll horizontally to read a line of text on supported screen sizes. Large Workflows on small monitors may require horizontal scrolling. | |||
1.4.9 Images of Text (No Exception) (Level AAA) | Supports | No images of text are used. Users are responsible for their own content selection and alternatives. | |||
2.1.3 Keyboard (No Exception) (Level AAA) | Supports | No timeouts on input are not imposed without customization. | |||
2.2.3 No Timing (Level AAA) | Supports | See 2.2.1 Remarks. | |||
2.2.4 Interruptions (Level AAA) | Supports | Interruptions can be postponed or suppressed by the user (login obviously excepted). | |||
2.2.5 Re-authenticating (Level AAA) | Supports | Document editing is auto saved every keystroke to Web Browser Storage, and users are prompted to recover for convenience. | |||
2.2.6 Timeouts (Level AAA 2.1 only) | Supports | " | |||
2.3.2 Three Flashes (Level AAA) | Supports | See 2.3.1 Remarks. | |||
2.3.3 Animation from Interactions (Level AAA 2.1 only) | Supports | prefers-reduced-motion is respected. | |||
2.4.8 Location (Level AAA) | Supports | breadcrumb trails are provided. | |||
2.4.9 Link Purpose (Link Only) (Level AAA) | Supports | See 1.3.6 Remarks. | |||
2.4.10 Section Headings (Level AAA) | Supports | ||||
2.5.5 Target Size (Level AAA 2.1 only) | Supports | Target size is increased automatically when lower accuracy input is detected. Can also be forced/customized | |||
2.5.6 Concurrent Input Mechanisms (Level AAA 2.1 only) | Supports | multiple concurrent input types are supported. | |||
3.1.3 Unusual Words (Level AAA) | Supports | Via select > right click > search web for. Abbreviations, idioms, and jargon are avoided. | |||
3.1.4 Abbreviations (Level AAA) | Supports | " | |||
3.1.5 Reading Level (Level AAA) | Supports | Common words are used where long explanations of technical terms would not be required | |||
3.1.6 Pronunciation (Level AAA) | Supports | See 1.3.1 Remarks. | |||
3.2.5 Change on Request (Level AAA) | Supports | See 2.2.1 Remarks. | |||
3.3.5 Help (Level AAA) | Partially Supports | There are select help icons and paragraphs in some contexts for clarity. | |||
3.3.6 Error Prevention (All) (Level AAA) | Supports | See 3.3.4 Remarks. | |||